The Complete Guide to Web3 Auth
Web3 auth is one of the most under-appreciated, yet powerful features of the blockchain — enabling users to sign into any app or website across the web through a single, digital, interoperable identity.
Gone are the days of users having to make separate accounts for every single app or website they interact with, all of which are centrally-controlled and prone to data leaks & hacks.
In this blog post, we’re going to dive into everything you need to know about web3 auth. We’ll cover what web3 auth is & how it works under the hood, why it’s better than web2 auth solutions like OAuth, and why you may consider integrating web3 auth into your app to better acquire & onboard users. Let's dive in.
What is Web3 Auth?
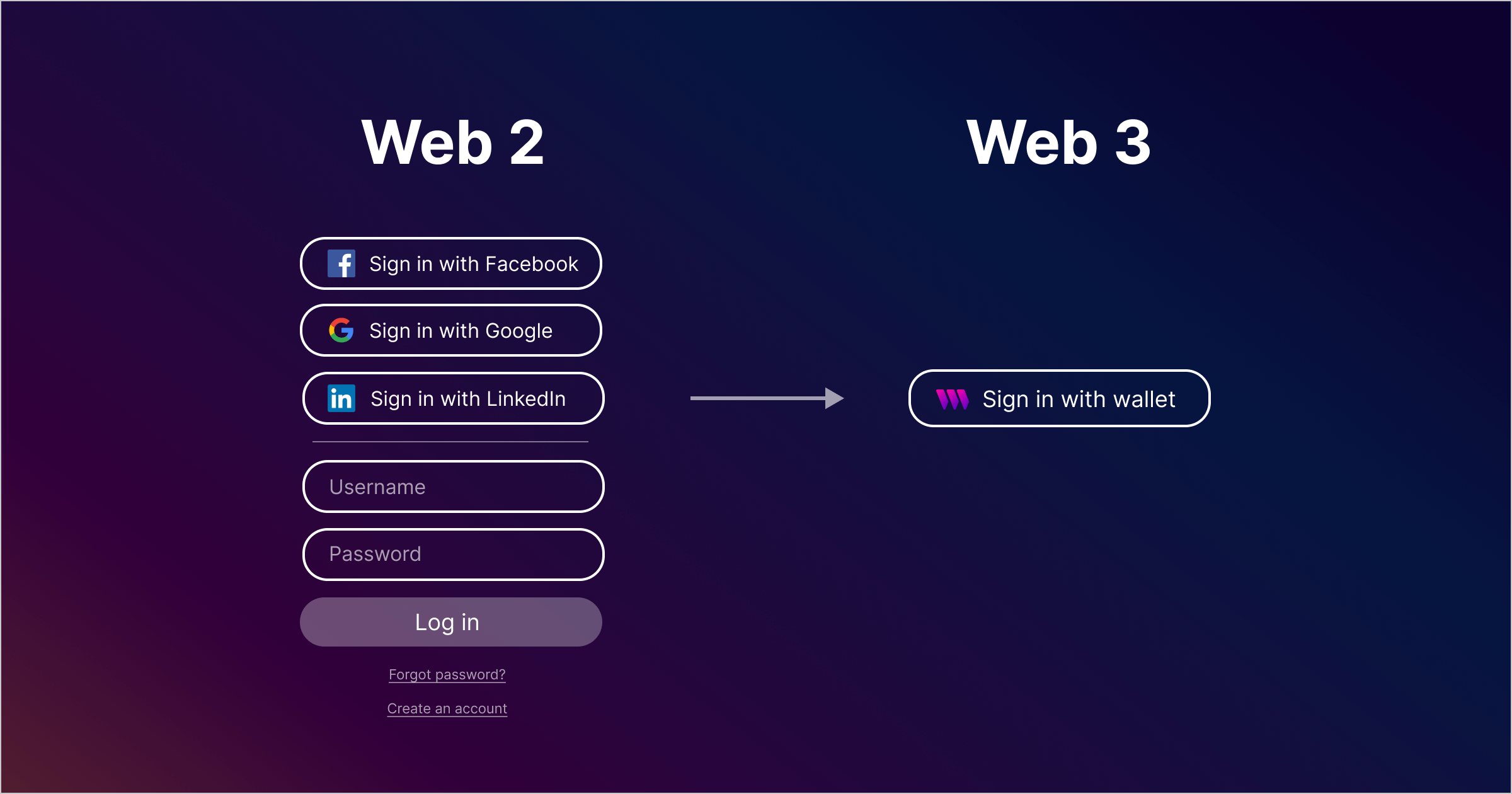
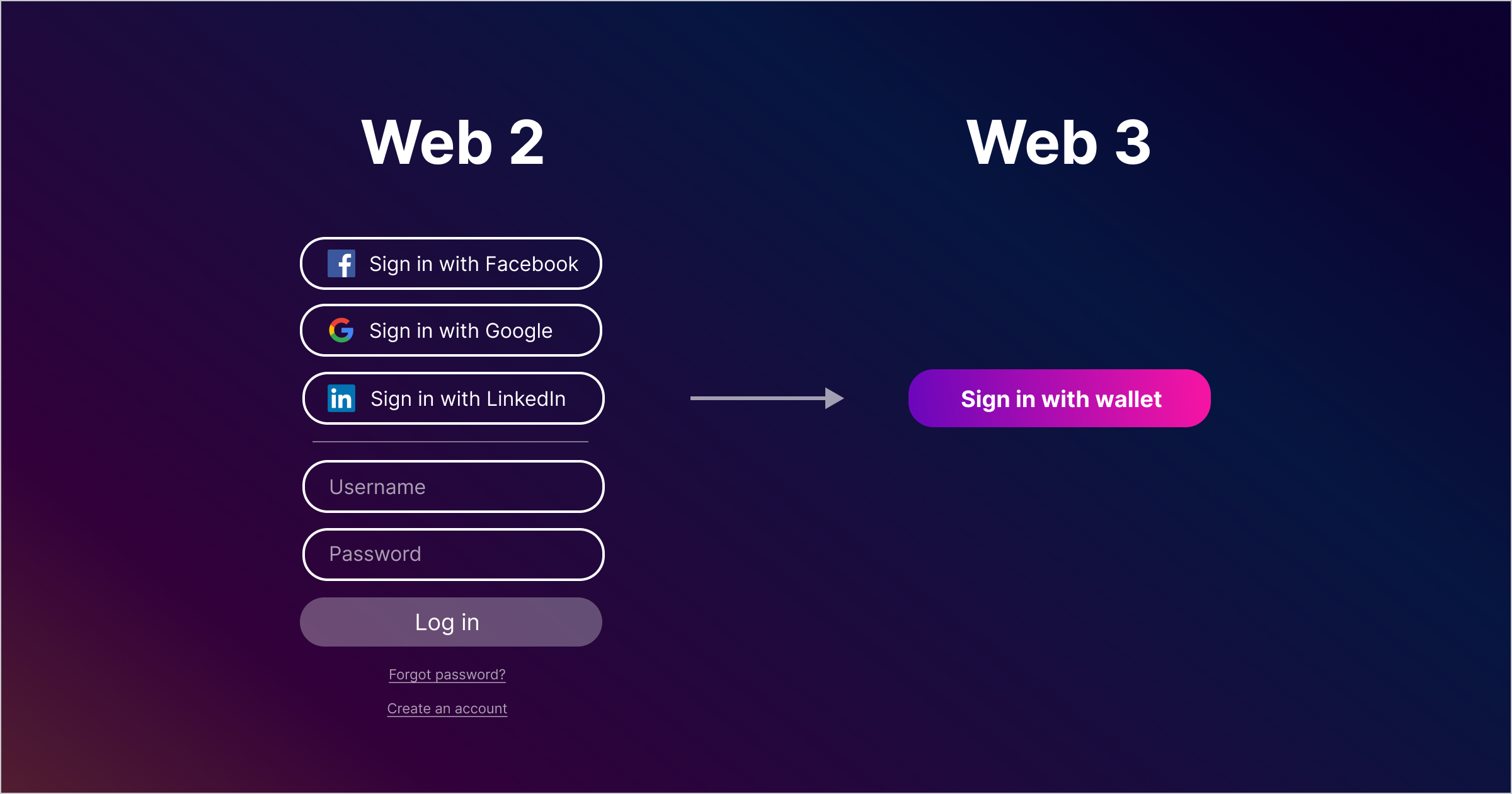
Web3 auth is the process in which a user verifies their “identity” by connecting their cryptocurrency wallet to an application, rather than logging in with a username and password. This allows users to more seamlessly interact with an application, which results in less friction & a smoother onboarding process.
While the premise of web3 auth is simple, the blockchain brings powerful capabilities to user login solutions that will forever change the way authentication works in modern applications.
To better understand this, let's first take a closer look at the way traditional auth solutions work today — and how they compare to authentication enabled by the blockchain.
How does web2 authentication work?
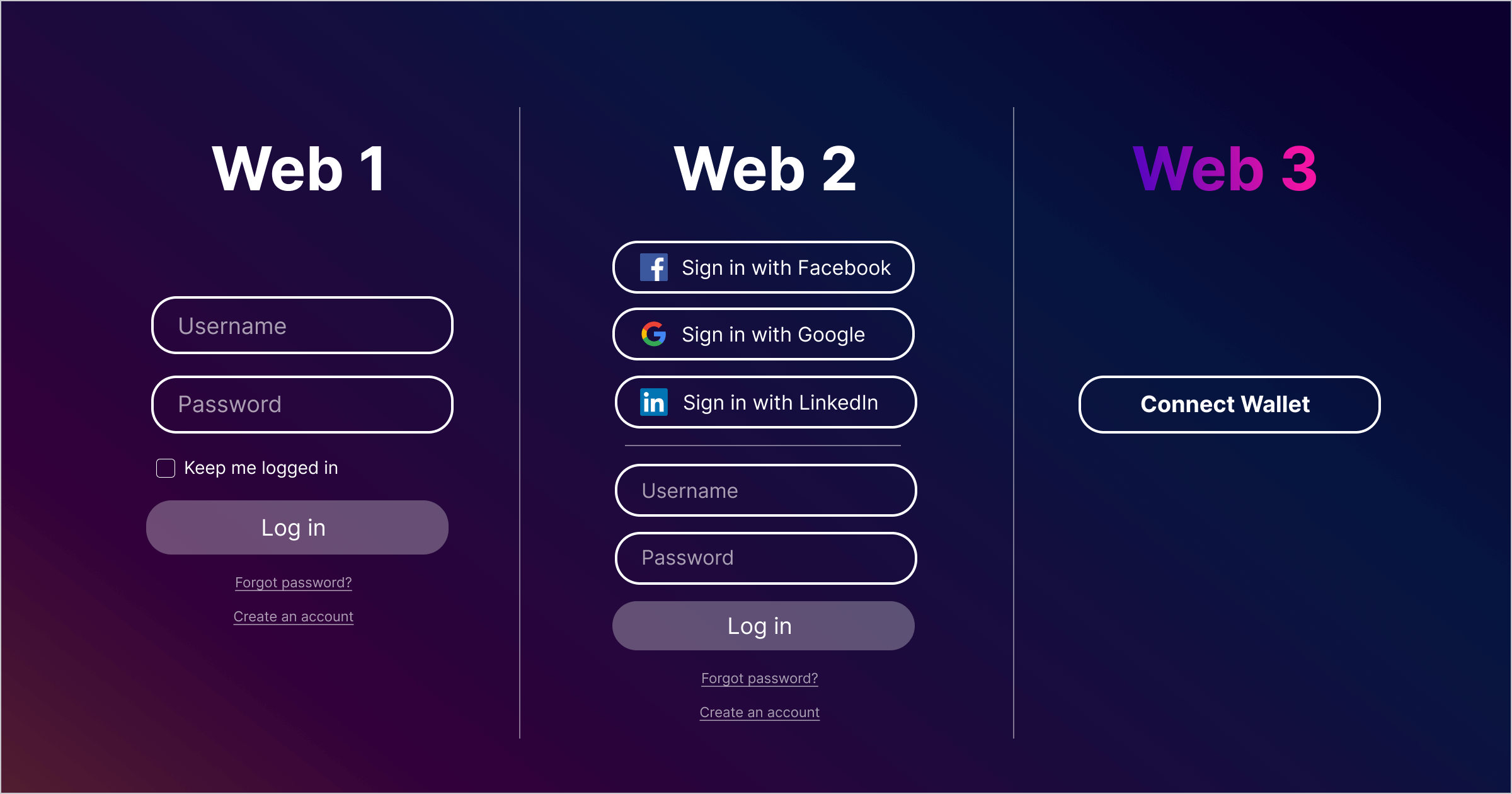
Traditional web2 authentication typically works by having the user provide a set of credentials, such as a username and password, to access and interact with an app or website. The app or website then checks the provided credentials against a database of authorized users to verify the identity of the user. If the provided credentials match a set of stored credentials, the user is granted access to the site.
To enhance security, many websites now employ additional measures such as multi-factor authentication, which requires the user to provide multiple forms of identification, such as a password and a one-time code sent to their phone. This makes it more difficult for an attacker to gain unauthorized access, even if they have obtained the password through hacking or social engineering.
But traditional authentication solutions have remained mostly the same for over a decade, and they come with many disadvantages that haven't previously been solved for.
Why doesn’t web2 authentication cut it?
Authentication is a crucial part of online security, as it helps to protect sensitive information and prevent unauthorized access to sensitive data. But the username-and-password approach of web2 authentication isn’t enough to protect users, and comes with many disadvantages:
- Tedious username and password management: Users are required to create unique usernames and passwords for each application they use. Keeping track of so many login credentials can be tedious, which leaves many opting to use the same ones across accounts — posing a security risk. This also increases friction in the onboarding process for users.
- Centralized control of user data: When user data is stored in centralized servers, it is prone to potential hacks or breaches — which can result in the theft of login credentials, personal information, and financial data. Users must also trust third-party providers to manage their data & protect their privacy — but many of those providers maliciously collect, share, and sell users' data.
- Phishing attacks: Phishing attacks, in which attackers try to trick a user into revealing their username and password, are an increasingly-common threat across the web. If a user falls for a phishing attack, their credentials can be used to gain unauthorized access to their accounts.
What about OAuth?
OAuth (or Open Authorization) is a protocol that attempts to solve this by allowing users to authenticate for an app or website through login credentials from another — without having to share those credentials with the app.
OAuth is widely used by web & mobile applications, and is supported by major services like Google, Facebook, Twitter, & Microsoft. This is what a user login with OAuth integrated typically looks like:
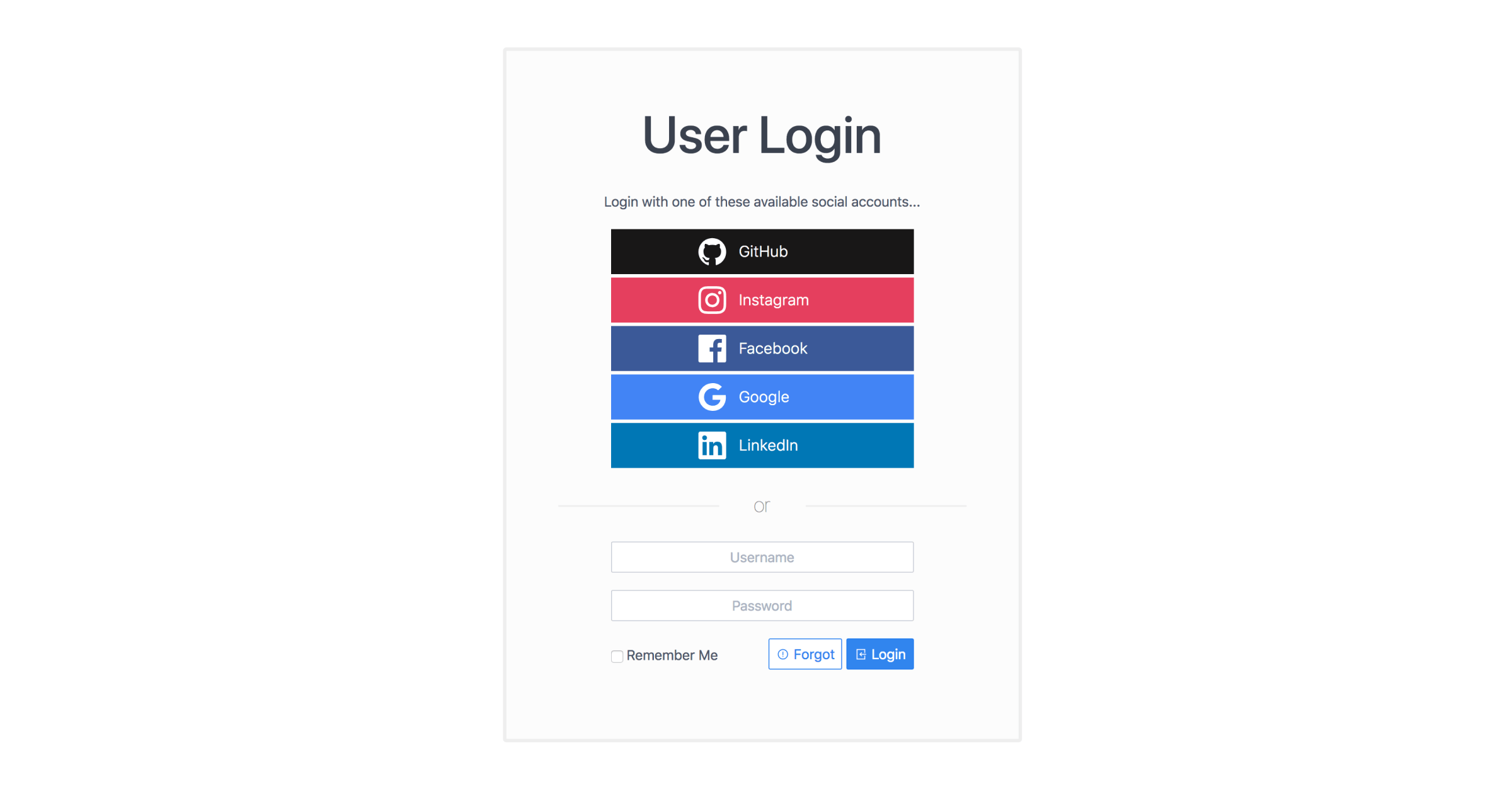
Aside from the overwhelming user interface above, OAuth has similar problems to other web2 authentication solutions:
- Users aren't always aware of what information they're sharing or granting access to with the third-party app or website.
- Users must give up control of their data and privacy to the third-party app — which can store or share the data in a way that the user does not intend or approve.
So if centralized control of user data in web2 login solutions leads to security risks, privacy concerns, and a poor user experience — what's the solution? Enter web3 auth.
How does Web3 Auth work?
Here's how web3 auth works:
- Key Generation: A user generates a unique pair of public and private keys, which serve as their digital identity in the web3 ecosystem. The private key is kept secret by the user and is used to sign transactions and access their accounts. The public key is shared publicly and is used to identify the user.
- Signing In: To sign in to a dApp, the user uses their private key to sign a cryptographic message, proving that they are the owner of the associated public key. This process is known as signing in with a digital signature.
- Access Control: The dApp can then use the public key to verify the user's digital signature and grant or deny access to their data based on the permissions set by the user.
In web3 auth, users have complete control over their data and can grant or revoke access to it as they see fit. This offers a high degree of privacy and security, as users do not need to rely on centralized third-party services to manage their data.
Learn more about how web3 auth works under the hood:
What are the advantages of Web3 Auth?
Web3 authentication uses decentralization to offer several key advantages compared to traditional authentication methods:
- Increased security: By relying on cryptographic keys to authenticate users, rather than a centralized third-party service, web3 authentication provides a higher level of security. Users have complete control over their own data and can grant or revoke access to it as they see fit, reducing the risk of unauthorized access or data breaches.
- Better user experience: Web3 authentication eliminates the need for users to create and remember different usernames and passwords for each individual app or service. This can result in higher user engagement and retention for dApps.
- Interoperability: Web3 authentication provides users with a unified digital identity that is interoperable across different dApps — allowing for a new dApp to build an engaged & curated audience by giving access, or perks that cause delight, to holders of a specific NFT or token.
- Token-gated functionality: Web3 authentication enables dApps to token-gate exclusive functionality, granting access only to holders of specific tokens — delighting users with immersive web3 experiences & enabling new monetization models for companies.
- True privacy: Web3 authentication is designed to protect user privacy by giving users control over their own data and limiting the amount of information that is shared with third-party apps and services. Users can interact with applications completely anonymously, or pseudonymously, without having to reveal sensitive details about their identity.
How do I integrate Web3 Auth into my app or website?
Using thirdweb Auth, you can easily integrate web3 auth into your website or application. Our SDK allows you to connect to all of the most popular wallets:
And we have various guides on how to integrate web3 auth based on your use case:



Conclusion: Why Web3 Auth is the future
All in all, web3 auth offers a decentralized, user-controlled authentication solution that changes the way users are authenticated for modern applications. It provides increased security & privacy, better user experiences, and a revolutionary way to unify & manage digital identities on the web — for businesses, developers, and users alike.
We hope this blog post has helped you better understand what Web3 Auth is, what its advantages are compared to traditional auth solutions, and why web3 auth is a paradigm shift in user authentication for modern applications.
If you have any questions, join 32,000+ other builders on our Discord community — or if you'd like more info on how we can help your business with web3 auth, reach out directly!

